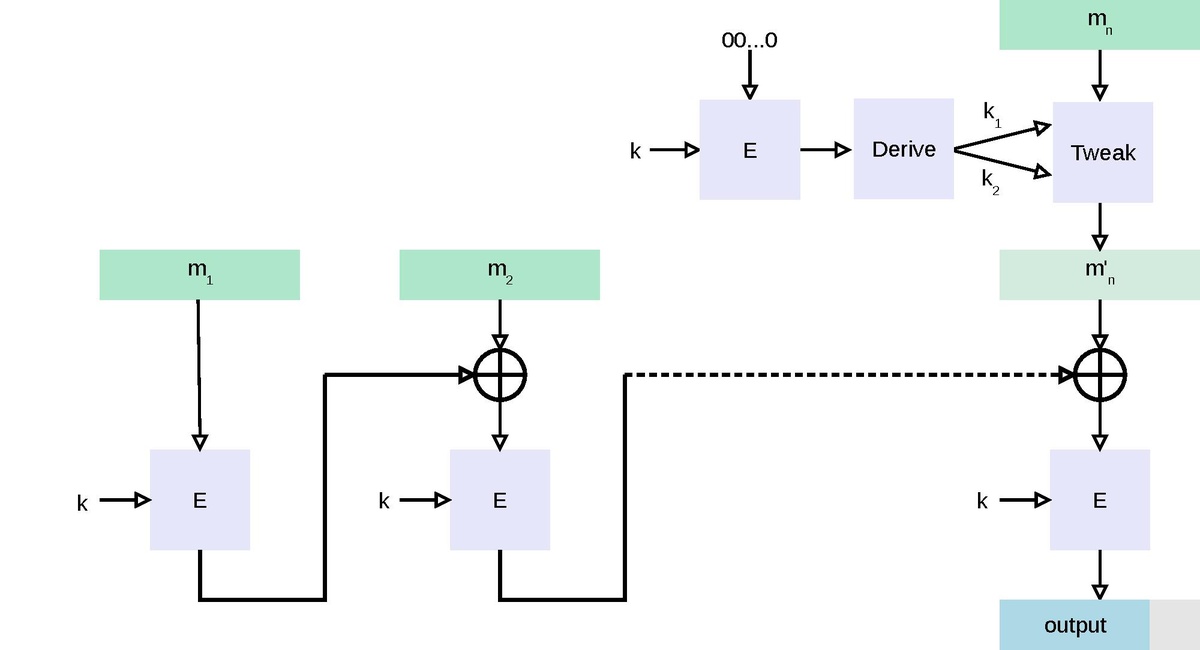
Attacks on the RawCBC-MAC if the final step of encrypting with a second key isn't done - Cryptography Stack Exchange
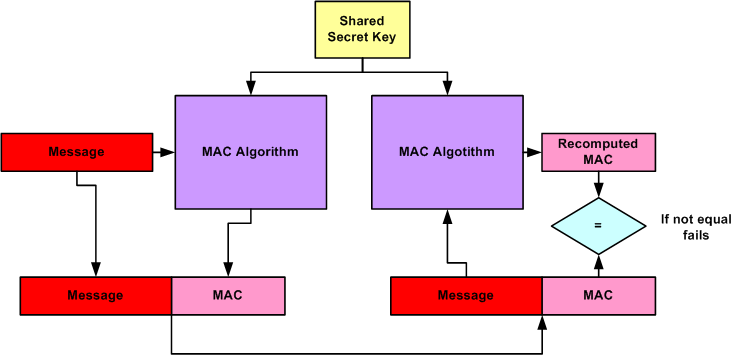
GitHub - NilFoundation/crypto3-mac: Message authentication codes for =nil; Crypto3 cryptography suite
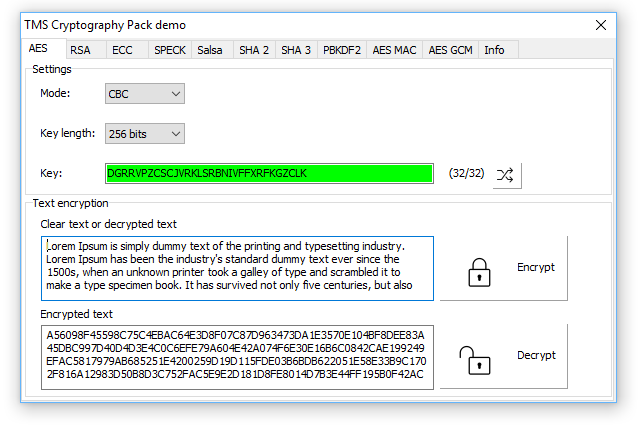
TMS Cryptography Pack Software library that provides various algorithms used to encrypt, sign and hash data.


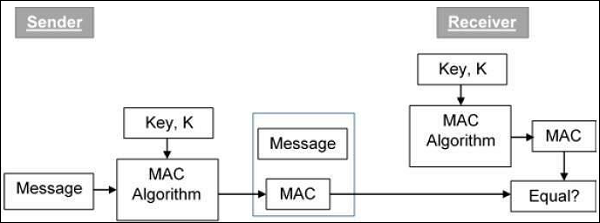

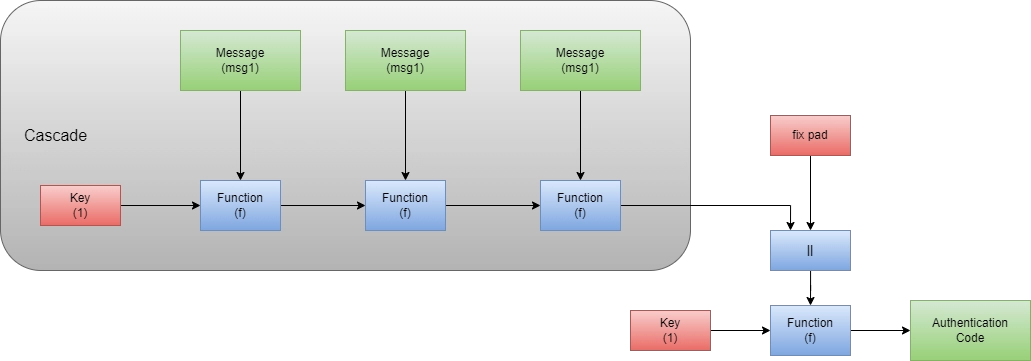





.svg/570px-CBC-MAC_structure_(en).svg.png)